Fausto Mendoza
INFORMATION TECHNOLOGY ENGINEER

© 2023 Fausto Mendoza
INFORMATION TECHNOLOGY ENGINEER
My objective is to ensure the organization’s information technology is secure while adding maximum value and facilitating the business’s success.
daily tasks: project management, implementing new technologies, designing, bridging systems, and managing complex systems over their life cycles. Administrating servers/workstations, cybersecurity, hardware, and software to ensure departments run smoothly.
• Virtual Infrastructure using Microsoft Hyper-V, vSphere
• Windows Server infrastructure services, including but not limited to, Active Directory, DNS, Group Policy.
• Linux Servers Administration - Suse, Red Hat, Ubuntu Server, Centos
• Network Engineer - Cisco, SonicWall, Juniper, Mikrotik, Ubiquiti, Linksys, Netgear, Cradlepoint, HPE, Ruckus, pfsence, Untangle - Static/DHCP Servers, RADIUS , MPLS, VPN, TCP/IP, VLANS. Site to Site IPsec, SOCKS v4/5
• Wireless technologies (WiFi, Bluetooth, NFC/RFID)
• Scripting in PowerShell, Bash, or Python
• Multilayer Fail-over and disaster recovery Acronis, Veeam, Barracuda.
• Database admin MSSQL/MySQL
• Apple Ecosystem Administration for In corporate environments
• Google suite and Office 365 migrations and administration
• Cloud - Amazon Web Services, Google Cloud Platform, Microsoft Azure.
•Project Management - Site survey and blueprints. Guide team members to accomplish all project goals within parameters. Documenting all steps. Working with third parties to complete objectives.
• MSP software - TeamViewer itbrain, ConnectWise and proprietary ticketing systems
• Website/e-commerce implementation and project planning with PCI compliance
• e-commerce inventory and finance integration
• Multi payment gateway integration
• Knowledge of the following technologies: Visual Studio, JavaScript, jQuery, HTML 5, CSS, XML, PHP.
• SQL database analysis and design T-SQL, Stored Procedures and Triggers.
• Cybersecurity regarding Virus, Malware, Ransomware and Firewalls.
• Risk assessment, audit, and IT security assessments local and foreign.
• Forensic research, designing security architectures, developing policies, gathering metrics, and reporting status.
• Web-related technologies (Web applications, Web Services, Service-Oriented Architectures) and of network/web related protocols.
• Vulnerability management tools. (eg. Linux Kail, Linux Blackarch)
• Educating people on best security practices for the organization (phishing emails, scams, attaching unknown devices and targeted social engineering attacks)
• Department of Defense policy, FCC, PCI, HIPAA compliance implementation.
• Cabling, installing, configuring, and troubleshooting low voltage networks for new and existing.
• Rack installation and design for AV, network, and telecom for commercial and high-end homes.
• Expertise in using tools such as labelers, oscilloscopes, multimeters, and network analyzers.
• Proficient in the installation of network infrastructure including switches, and routers.
• Telecom installations for PBX, VOIP/Analog, account LOA management, and turn-up.
• Communicate with customers to gather information and provide technical support.
• Test fiber and copper networks for the turn-up.
• WAP install and optimizations.
• Read and create blueprints.
IT Managed Service Provider & Virtual CIO for small to minimum size businesses. Providing IT services to large enterprise entities based on active projects.
Oversee the use of Information technology (IT) in the company. Devise the company’s IT strategy and ensure that all systems necessary to support it's operations and objectives are in place.
Setting up workstations with computers and necessary peripheral devices. Checking computer hardware (HDD, mouses, keyboards etc.) to ensure functionality. Installing and configuring appropriate software and functions according to specifications.
Radio VHF/UHF frequency programming Project 25 (P25) APCO 25 and ASTRO 2 with military-grade encryption and FCC rules and regulations.
Website and social media content via photography, video and graphic design
VoIP/IP telephony integrations for business telephone systems, cordless phones, mobile devices and desktop/laptop computers.
Boosting engagement and conversion rate
SEO best practices to improve ranking
Crestron Core Certification Installer, Design Engineer, and Programmer for smart integration in commercial and residential. QSC design and programming Q-SYS Designer.

Slow speeds, Connection lost, WiFi outage! I was sent for a network take-over at one of the client’s locations to set up a site-to-site connection. When I walked up to the network rack in the basement I was shocked it was working at all. The network was a mix of outdated consumer and enterprise equipment. […]
Read More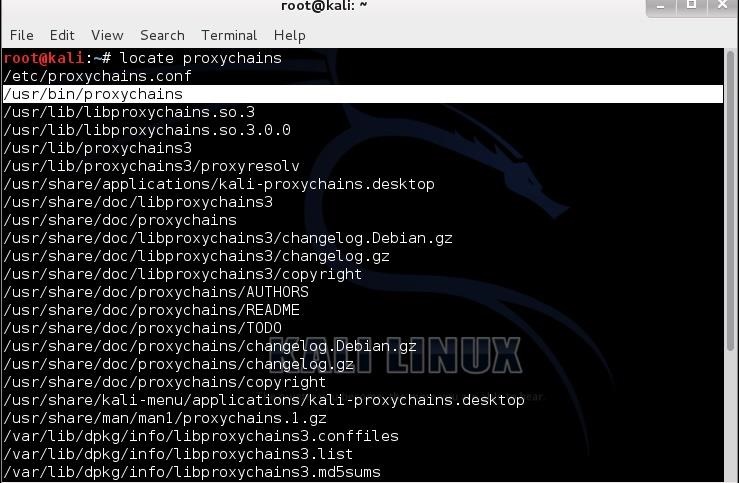
I experienced this DoSS attack first hand. R-U-Dead-Yet, or RUDY for short, implements the generic HTTP DoS attack via long form field submissions. RUDY attack targets web applications by starvation of available sessions on the web server. RUDY keeps sessions at halt using never-ending POST transmissions and sending an arbitrarily large content-length header value. I […]
Read More
Leadership is not about a title or a designation. It's about impact, influence and inspiration. Impact involves getting results, influence is about spreading the passion you have for your work, and you have to inspire team-mates and customers.
Mike Izzo – General Manager Major Surplus and Survival
435 W. Alondra Blvd.
Gardena, Ca 90248
310-324-8855 x 138
majorsurplus.com
David Smith – Retail Store Manager
Major Surplus and Survival
435 W. Alondra Blvd.
Gardena, Ca 90248
3103248855 x 124
majorsurplus.com
Carla Marron – Customer Service Specialist
Major Surplus and Survival
435 W. Alondra Blvd.
Gardena, Ca 90248
3103248855 x 107
majorsurplus.com