I experienced this DoSS attack first hand.
R-U-Dead-Yet, or RUDY for short, implements the generic HTTP DoS attack via long form field submissions.
RUDY attack targets web applications by starvation of available sessions on the web server.
RUDY keeps sessions at halt using never-ending POST transmissions and sending an arbitrarily large content-length header value.
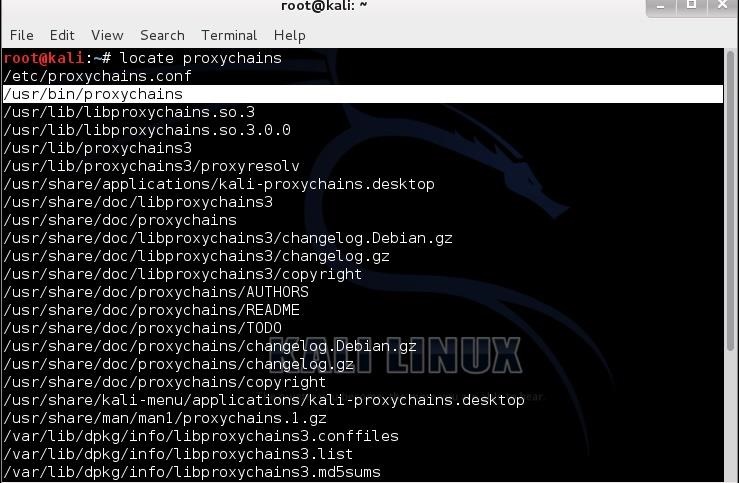
I was able to track the attack from different IP addresses corresponding to public socks5 proxy servers. A proxychain was at play masking the attack. String multiple proxies in a chain, make it harder and harder to detect the original IP address.
I was able to flip on cloudflare on a DNS level. Blocked the the IP ranges that in logs.
Lost of revenue was minimal.

You must be logged in to post a comment.